Understanding L2Beat (1): Introduction and Risk Assessment Framework
Notes to readers: This article is an English adaptation of my original Chinese piece on L2Beat analysis written in 2025. I've translated, restructured, and expanded the content to make these Layer 2 evaluation concepts more accessible to a broader audience while preserving the technical accuracy of the original work. This is the first part of a three-part series that will help you navigate and understand L2Beat's comprehensive analysis platform.
TL;DR
L2Beat is the most comprehensive platform for analyzing Ethereum Layer 2 solutions, providing detailed risk assessments across five critical areas: state validation, data availability, exit windows, sequencer failure, and proposer failure. Understanding L2Beat's risk framework helps users evaluate the security trade-offs between different L2 approaches—from Rollups that post all data on-chain for maximum security, to Validiums and Optimiums that use external data availability for lower costs but additional trust assumptions.
What is L2Beat and Why It Matters
L2Beat serves as the definitive resource for understanding Ethereum's Layer 2 ecosystem. It provides comprehensive documentation of virtually all L2 solutions, tracking everything from Total Value Locked (TVL) and transaction throughput to technical architecture details, contract addresses, admin permissions, and most importantly—security risks and maturity assessments.
Beyond individual L2 analysis, L2Beat also covers cross-chain bridges and Data Availability (DA) solutions, offering a complete picture of the scaling infrastructure built around Ethereum. However, interpreting L2Beat's various metrics, classifications, and risk assessments requires understanding the nuanced trade-offs that different L2 approaches make.
Before diving in: Readers should understand the basics of Rollups and Data Availability.
Note: This analysis references L2Beat's interface as of April 2025. The platform continuously evolves, so future updates may change the appearance from the screenshots referenced here.
L2Beat's Core Attributes: Your Navigation Guide
Before exploring the details, it's essential to understand the four key attributes L2Beat displays for each Layer 2 solution. These attributes form the foundation of L2Beat's analysis framework and will be covered throughout this series:
RISKS: Security assessment across five critical dimensions (covered in this article)
TYPE: The underlying technology approach - ZK or Optimistic (covered in Part 2)
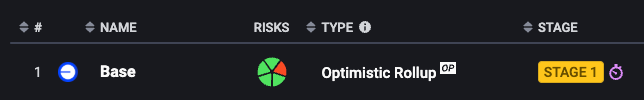
STAGE: Rollup maturity and decentralization level, with three stages from 0-2 (covered in Part 2)
DA LAYER: Where non-Rollup solutions publish their data (covered in Part 3)
Important note: Currently, only Rollups display a STAGE rating. Non-Rollup solutions (Validiums and Optimiums) show their DA LAYER instead, indicating where they store transaction data.
Understanding these four attributes helps you quickly assess any L2's security model, technological approach, maturity level, and trust assumptions. Let's start with the foundation—the RISKS framework.
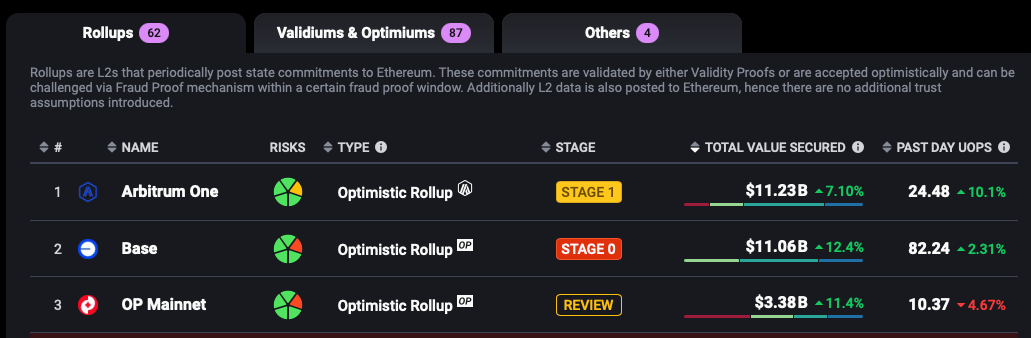
Understanding L2 Classifications
L2Beat organizes Layer 2 solutions into three main categories based on their data publication strategy, each representing different security and cost trade-offs.
Rollups: Maximum Security with On-Chain Data
Rollups represent the gold standard for L2 security by posting all transaction data directly to Ethereum (L1). This approach ensures:
Complete data availability: Anyone can reconstruct the L2 state from L1 data
Minimal trust assumptions: No reliance on external parties for data storage
Inherited security: Full benefit of Ethereum's consensus security
The trade-off is higher costs due to L1 data storage expenses, but this provides the strongest security guarantees.
Validiums & Optimiums: Lower Costs with External Data
Validiums and Optimiums reduce costs by storing data off-chain or on alternative data availability layers instead of Ethereum. While this significantly lowers transaction fees, it introduces additional trust assumptions:
Users must trust external data providers to remain honest and available
Additional complexity from cross-chain data verification mechanisms
Others: Incomplete Security Models
The "Others" category includes L2 solutions that lack essential security components:
Missing or incomplete proof systems (neither ZK proofs nor fraud proof challenge mechanisms)
Insufficient data availability guarantees
These solutions may offer high performance but compromise on the security guarantees that define genuine Layer 2 scaling.
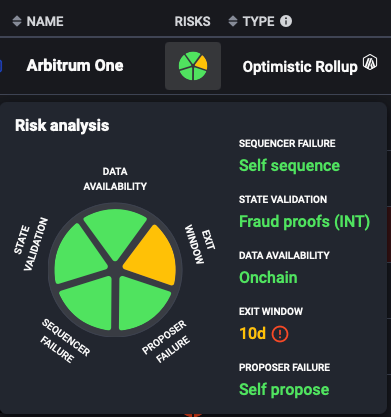
The RISKS Framework: Five Critical Security Dimensions
L2Beat's RISKS assessment evaluates each L2 across five fundamental security aspects: “STATE VALIDATION”, “DATA AVAILABILITY”, “EXIT WINDOW”, “PROPOSER FAILURE” and “SEQUENCER FAILURE”. Understanding these dimensions helps users make informed decisions about which L2s align with their security requirements and risk tolerance.
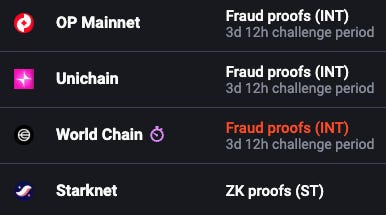
1. STATE VALIDATION: How L2 State Correctness is Ensured
This measures how the L2 proves that its state transitions are correct and valid.
🟢 Green: Working ZK Proofs or Fraud Proofs
🟡 Yellow: Working Fraud Proofs but challengers are whitelisted
🔴 Red: No working proofs or the number of whitelisted fraud proof challengers is too small or challengers are not external entity (external to Rollup operator)
Technical Detail: The assessment also notes whether fraud proof systems use single-round (1R) or interactive (INT) challenge mechanisms, with challenge period lengths clearly specified.
2. DATA AVAILABILITY: Where Transaction Data is Stored
This evaluates where and how transaction data is made available for verification.
🟢 Green (On-Chain):
"Onchain": All data posted to Ethereum with no additional trust assumptions
State Diff notation (SD): Some Rollups post compressed state differences instead of full transaction data, reducing costs while maintaining security
🔴 Red (External):
"External": Data stored on alternative DA layers or with third parties
Key Insight: Only ZK Rollups can safely use State Diff approaches without compromising security, as their cryptographic proofs guarantee state correctness regardless of data compression methods.
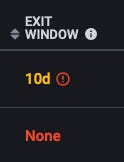
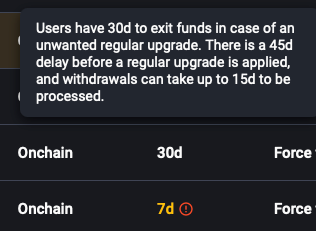
3. EXIT WINDOW: Protection Against Malicious/Unfavorable Upgrades
This measures how much time users have to exit an L2 if they disagree with a proposed upgrade.
🟢 Green (Sufficient Time):
Adequate exit window: Enough time for users to submit withdrawal requests and complete exits to L1
🟡 Yellow (Emergency Override):
Security Council powers: Emergency committees can accelerate upgrades
🔴 Red (Immediate Upgrades):
No exit protection: Upgrades take effect immediately
Special Case: Immutable contracts receive infinite exit windows since they cannot be upgraded maliciously.
4. SEQUENCER FAILURE: Censorship Resistance Mechanisms
This assesses what happens when the entity responsible for ordering transactions (the sequencer) goes offline or censors users.
🟢 Green (Self Sequence):
Force inclusion: Users can submit transactions directly to L1
Autonomous completion: Users can complete transaction inclusion after delays without sequencer
🟡 Yellow (Enqueue via L1):
Partial force inclusion: Users can submit transactions to L1 but cannot guarantee processing
Sequencer discretion: Sequencers can choose whether to process queued transactions
Example: ZKsync currently falls into this category—users can queue transactions, but sequencers can ignore them indefinitely
🔴 Red (No Mechanism):
Complete dependence: No way to bypass centralized sequencers
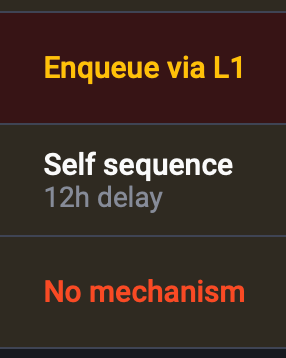
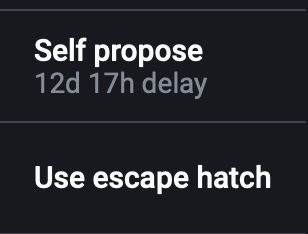
Special Mechanism - Force via L1: Some L2s implement "Escape Hatch" mechanisms where persistent censorship triggers complete L2 shutdown, allowing all users to exit with their assets.
More about Force Inclusion mechanism:
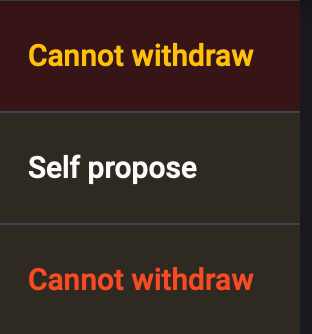
5. PROPOSER FAILURE: What Happens When State Proposers Stop Working
This evaluates backup mechanisms when the entities responsible for submitting L2 state updates to L1 become unavailable.
🟢 Green (Decentralized Backup):
Self propose: Anyone can step in as a proposer
Escape hatch: Systematic shutdown and user exit mechanisms
🟡 Yellow (Whitelist and Governance Backup):
Whitelisted proposers: Only approved entities can propose, but governance can change the whitelist
🔴 Red (Single Point of Failure):
Fixed proposer: No mechanism to replace failed proposers
What's Next
Understanding these risk fundamentals prepares you to evaluate specific L2 solutions effectively. In the next article, we'll explore L2Beat's type classifications (ZK vs Optimistic, Rollup vs Validium), the maturity STAGE framework that measures how decentralized a Rollup has become, and how to conduct deep-dive analysis of individual projects.
The risk framework we've covered here forms the foundation for all L2 evaluation—whether you're a user deciding where to bridge funds, a developer choosing where to deploy, or an investor analyzing the L2 landscape.
Coming up in Part 2: L2 Types, Maturity Stages, and Project Analysis - where we'll dive into the STAGE framework that measures Rollup decentralization and learn how to analyze specific L2 projects using Arbitrum as a detailed case study.